I am job hunting
I have recently been laid off, so like a lot of people in that position, I have been back on LinkedIn replying to random recruiters and product people who want to connect about future roles.
I hate this part of job hunting.
I would much rather get to a real interview, talk to actual people, and get a feel for the place. But when you are looking for work, you end up with a lot of chats going on at once, and you have to do a lot of hoop jumping just to get to the interview. You do not want to miss something real just because you were too slow to react.
That is exactly what these scams rely on.
Introducing Marc from Verse
Marc said he worked for a crypto company called Verse building in the RWA (real-world assets) space.
That was not a red flag to me at all. I have spent the last four years doing UI contracts for crypto companies, so this kind of outreach felt completely normal. I had two other legitimate crypto companies reach out to me that same week as well.
He said they were offering a part-time role, which immediately caught my attention because those are rare. I replied saying I would love to set up a call. He asked for my up-to-date CV, which I sent over, and then said he would send a quick 10–15 minute task for me to complete.
This was all relatively normal, though usually people would want to speak face-to-face before getting to this point. But this is tech, and honestly I was appreciating the messaging rather than endless amounts of calls.
The task
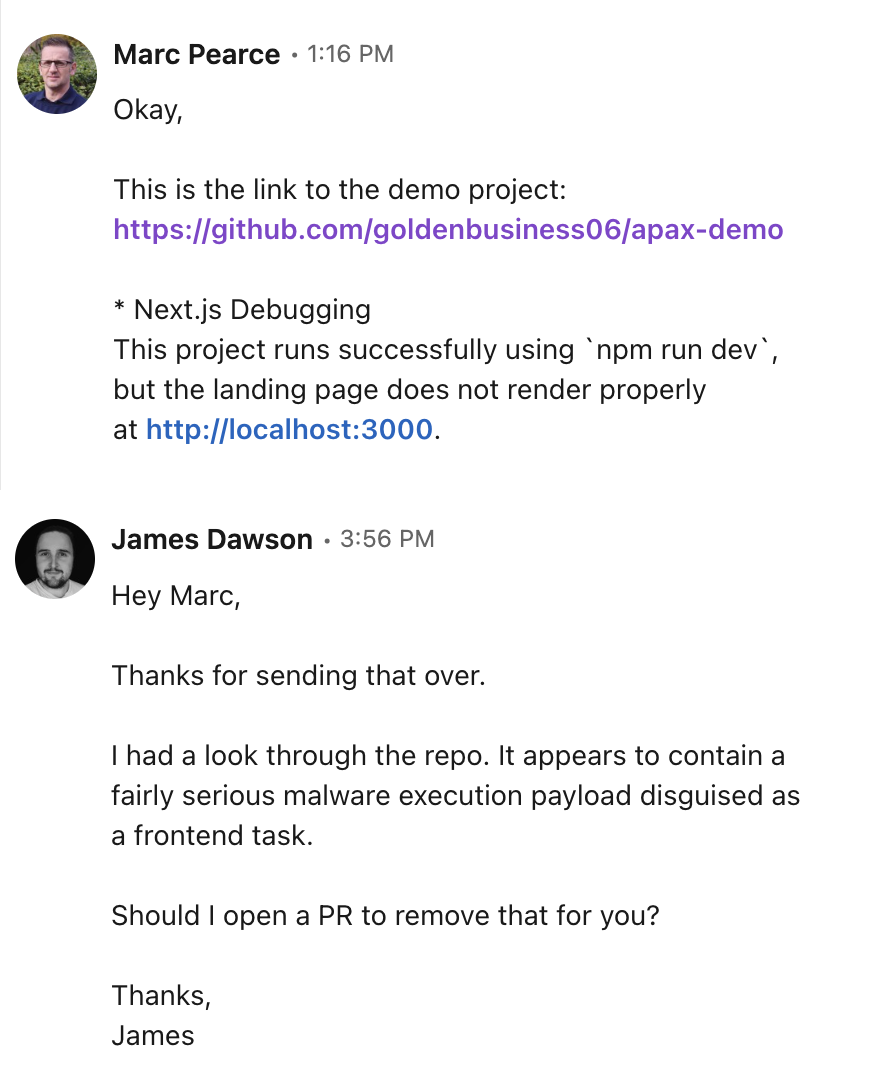
Here is the full message:
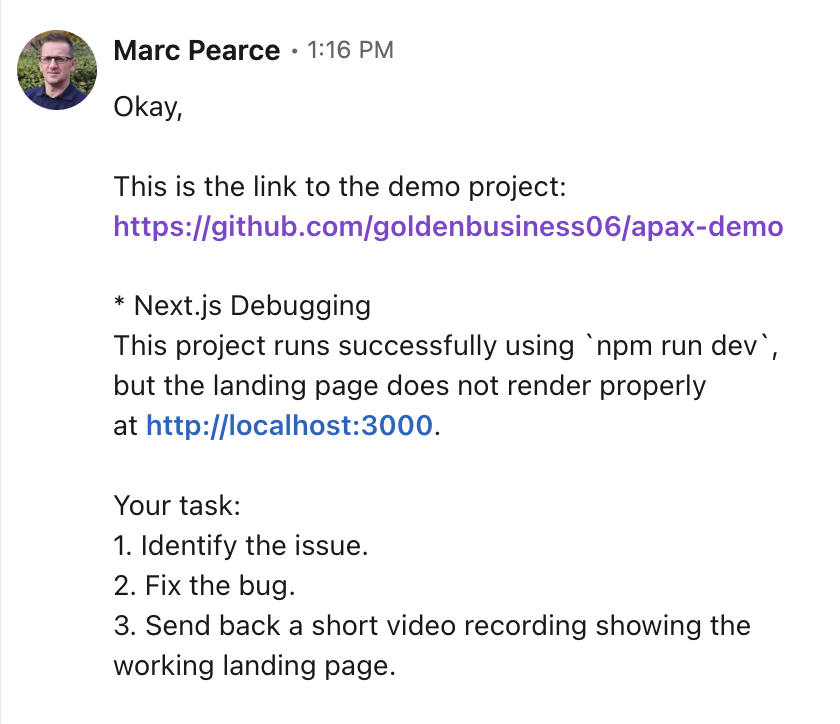
It was relatively normal, though I did feel like it was an exceptionally simple task for someone with 9 years of experience.
It was a Next.js app and it was using Hardhat, which is a very common Ethereum package. These are all things I have worked with before and am comfortable using.
Don't trust the internet
Growing up in the early 2000s, I saw the worst of the internet, and it burned me on multiple occasions.
One specific memory has permanently ingrained in me the idea that nothing from the internet should be installed or run on your machine without being thoroughly checked first. Back in the LimeWire days, while trying to download Age of Empires, I somehow managed to install a virus that permanently advertised a porn banner on the desktop of the family PC.
As you can imagine, that has stayed with me to this day.
Some instinct from those days was firing when I opened this repo and telling me I should check it before running anything locally.
What Claude found
The biggest red flag was this block:
This is a self-executing async function that runs the moment the module is imported. Here's the breakdown:
-
Decode the hidden URL — The environment variables (
DEV_API_KEY,DEV_SECRET_KEY,DEV_SECRET_VALUE) look innocent but are actually Base64-encoded strings. When decoded,DEV_API_KEYbecomes a URL pointing to a JSON blob hosted on jsonkeeper.com (which has since been removed but I managed to save it but will not share, if you are interested reach out to me). -
Fetch the payload — The code makes a GET request to that URL, passing along the decoded header values. The response contains a
cookiefield which holds the actual malicious JavaScript code as a string. -
Execute arbitrary code —
new Function("require", r)creates a new function from that string, andhandler(require)immediately executes it, passing in Node'srequireso the payload has full access to the file system, network, and everything else on your machine. -
Silent failure — The empty
catch (error: any) {}ensures that if anything goes wrong, you never see an error. The malware runs invisibly.
The genius of this approach is that the actual malicious code never exists in the repository. It's fetched at runtime from an external server, making it nearly impossible to detect by scanning the codebase alone.
It was able to detect the vulnerability in a fairly large codebase and show me the exact spot. Pretty amazing.
Always research the company
I should have checked their website before even chatting to this guy, but I only looked at their LinkedIn and treated that as the base check.
- Website: https://verselabs.org/
AI slop fest landing page. - Docs: https://verse-labs-foundation.gitbook.io/verselabs
AI slop fest docs.
But that is exactly how these scams work.
People looking for work are moving quickly. They are under pressure. They are stressed, vulnerable, and trying not to miss opportunities. If a message sounds plausible and vaguely matches their background, they are more likely to give it a chance.
There is also something deeply ingrained in me from trying to download video game torrents 20 years ago and ending up with a permanent porn banner installed on the family PC that I could not remove:
Never trust anything on the internet.
That instinct was firing pretty hard when I received a 0-star GitHub repo and was told to run it locally as part of a “simple Next.js debugging task.”
Marc specifically wanted me to get the landing page working, and at that point I knew something was weird. I have 9 years of professional experience, and this was such a laughably simple and pointless task that it would not prove anything meaningful to anyone.
That is why this kind of scam is so nasty. It does not just target technical weakness. It targets people at a moment when they are more willing to suspend doubt and keep moving.
Conclusion
I almost did something very stupid, but I was in a rush and I hate all the hoop jumping that has to happen when applying for new jobs.
Do not be like me.
Either run unknown code in a VM or in a sandboxed tool like CodeSandbox. Never just pull a random repo onto your machine and run it locally because someone claiming to hire you asked you to.
Hopefully someone reads this and avoids something catastrophic as well.
With the rise in AI, these scams are going to get more sophisticated, more believable, and more harmful.